En la actualidad, casi todas las empresas almacenan datos como usuarios, correos electrónicos, roles, impresoras, etc. en lo que se llama un servicio de directorio, lo que proporciona un acceso centralizado a los datos relacionados con la empresa que pueden utilizarse en todos sus sistemas. Una de las soluciones más utilizadas es Active Directory de Microsoft, ya que está estrechamente integrado con los sistemas operativos Windows. El otro LDAP, que significa Lightweight Directory Access Protocol, también tiene una amplia gama de usuarios desde el estándar de facto en los sistemas basados en Linux. Por lo general, queremos integrar LDAP con SAP BusinessObjects para permitir que los usuarios se autentiquen en la plataforma de BI, utilizando la misma contraseña que utilizan para iniciar sesión en otros sistemas de la empresa. Para hacerlo, SAP BO proporciona un módulo de autenticación LDAP en el CMC con un asistente fácil de seguir que facilita todos los pasos necesarios, que son los siguientes:
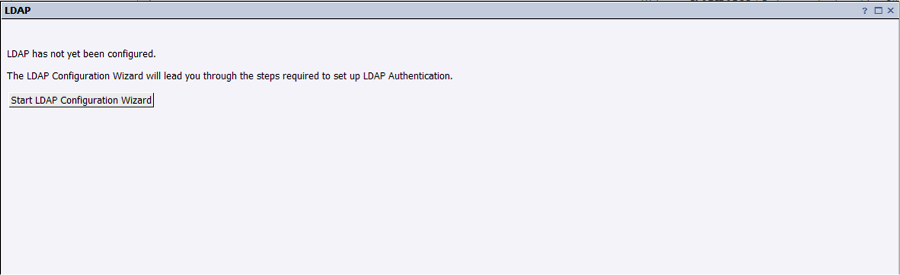
1. Login to CMC (localhost:8080/BOE/CMC) as an administrator and go to “Manage” -> “Authentication” section. Select “LDAP” and proceed to execute the wizard by clicking on “Start LDAP Configuration Wizard” 2. Enter the address of the LDAP servers and press “add”:
Esta información debe ser proporcionada por un administrador de red, ya que depende de la empresa y su despliegue de red.
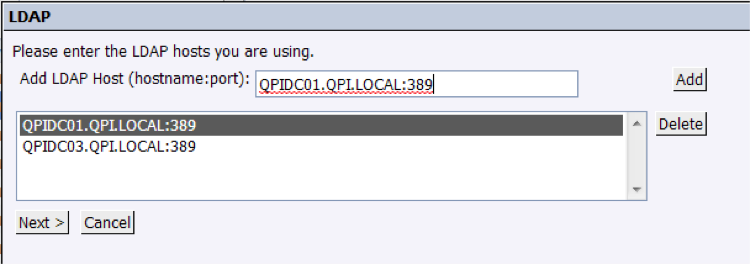
En el siguiente paso, seleccionaremos la solución tecnológica que implementa LDAP (LDAP es, como se indica en su nombre, sólo un protocolo). Esto es relevante porque dependiendo de la implementación, alguna información frecuente como nombre de usuario podría ser mapeada en un nodo diferente que otros. Como se indica en la captura de pantalla a continuación, se puede personalizar completamente, para que adaptemos el mapeo de LDAP a nuestra configuración de usuarios de BO:
En los cuadros de texto tenemos que introducir los nodos que se están utilizando en realidad en LDAP, o elegir los disponibles por defecto.
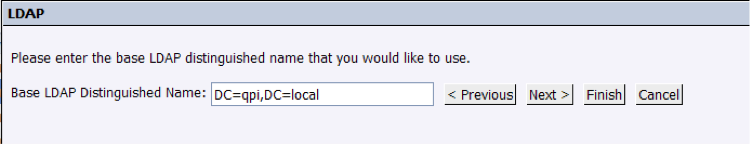
3. In this step we will set the Distinguished Name of the branch from which all the users are pending:
Esta información debe ser proporcionada por el administrador de la red.
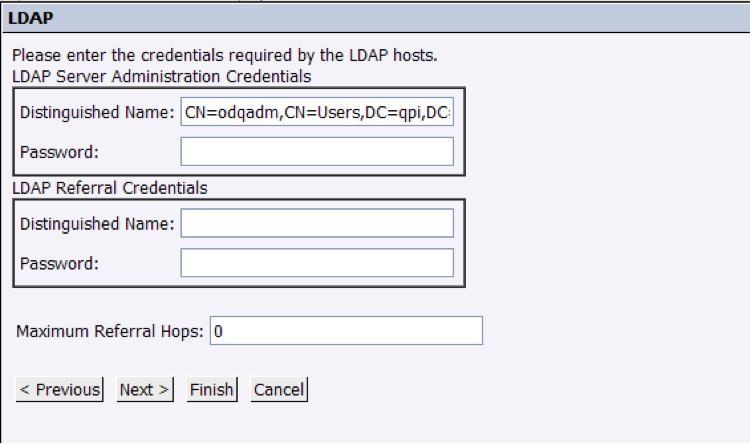
4. In next screen we will set up accounts with read access to LDAP servers. They do not have to have Administrator rights:
Asegúrese de que el nombre de usuario es un Nombre Distinguido, utilizando la notación LDAP, no sólo un simple nombre de usuario simple.
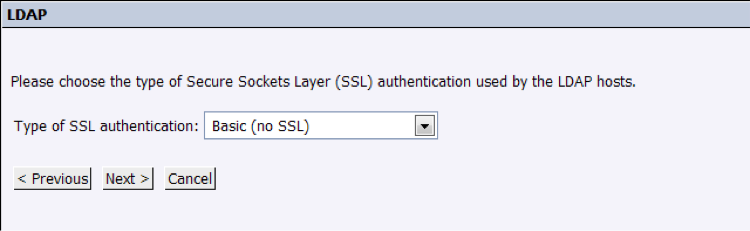
5. We will configure the security access to the LDAP server by selecting “Basic (no SSL)”, but it may change depending on the network configuration:
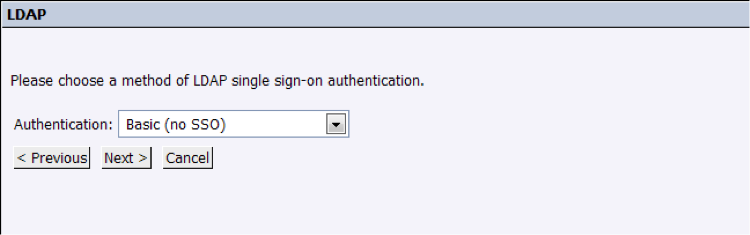
6. Same for this step, it may change depending on the customer, but usually selecting “Basic (No SSO)” should be fine. These settings can also be changed in the future, so proceed to the last screen:
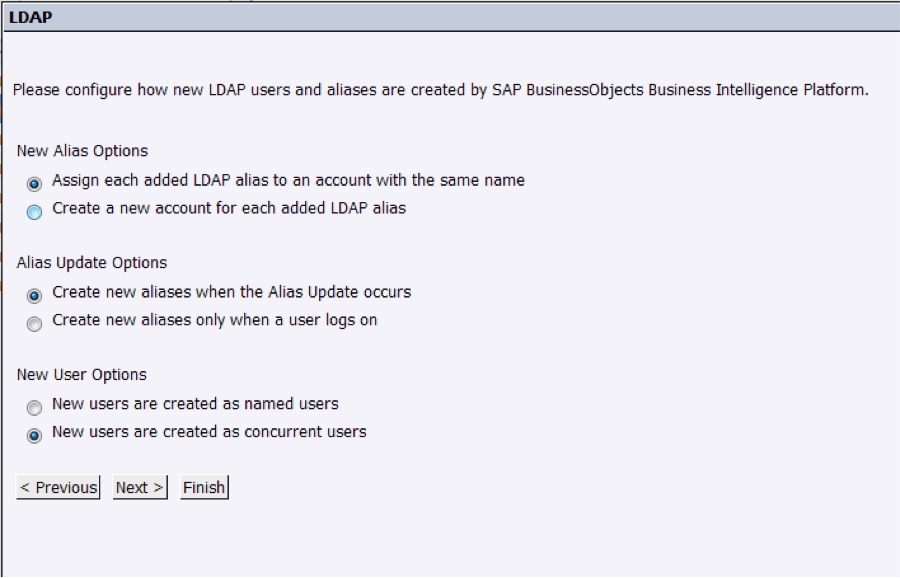
7. In the last screen, we will leave the configurations as follow:
Las opciones anteriores pueden variar según el cliente y se explican por sí mismas.
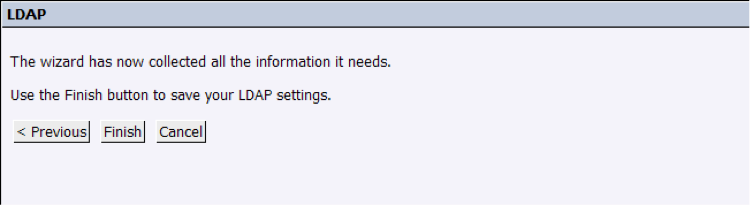
8. Finally, we will commit the changes by pressing “Finish”:
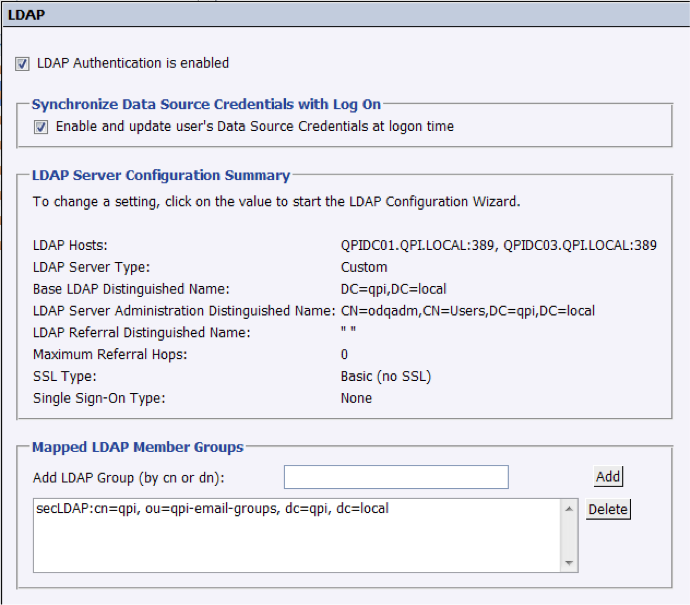
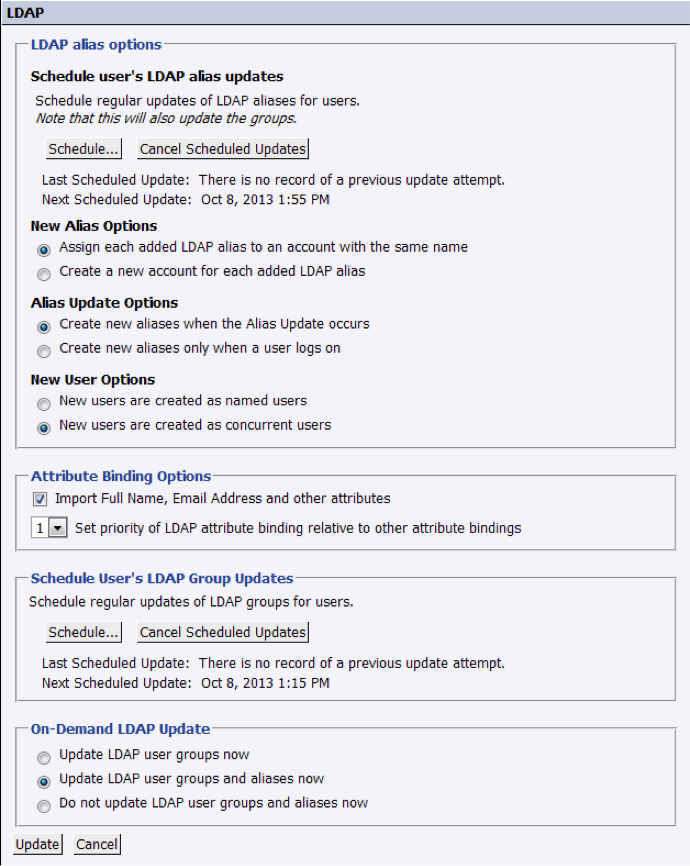
9. In the summary screen, we can review all the previous settings and configure the final steps:
- Programación de la sincronización de cuentas entre SAP BO y LDAP. Lo estableceremos para que se actualice cada hora, ya que es una consulta de menos de una segunda con una sobrecarga muy baja.
- Grupo de usuarios que vamos a importar. Lo que tenemos que hacer es elegir la rama LDAP que vamos a importar. Tiene que ser un nombre distinguido: "CN = XXX, OU = YYY-Email-Grupos, DC = ZZZ, DC = local". Esto significa que todos los miembros de este grupo tendrán acceso a SAP BO a través de LDAP.
A continuación encontrará la configuración final:
Esta pantalla de resumen le permite retroceder y revertir cualquier ajuste que no nos resulte cómodo.
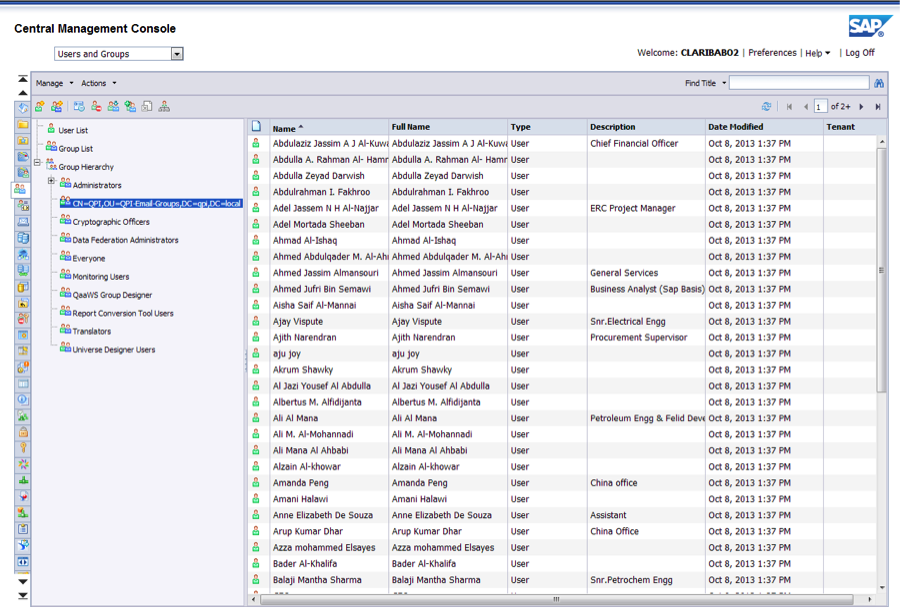
10. After doing the initial import, a group containing all new imported users will appear. To see it, go back to the home screen of the CMC and go to the “Users and Groups” section, under “Organize”:
Para evitar perder en cada sincronización los parámetros de seguridad del grupo, encapsularemos este grupo en un nuevo creado llamado "Enterprise" (puede escoger cualquier nombre). En este grupo implementaremos la seguridad real de los usuarios de LDAP:
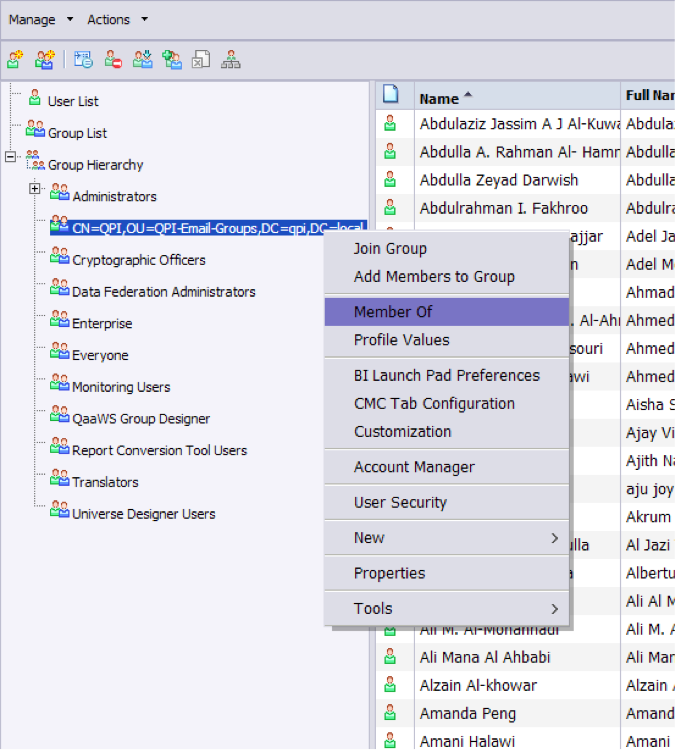
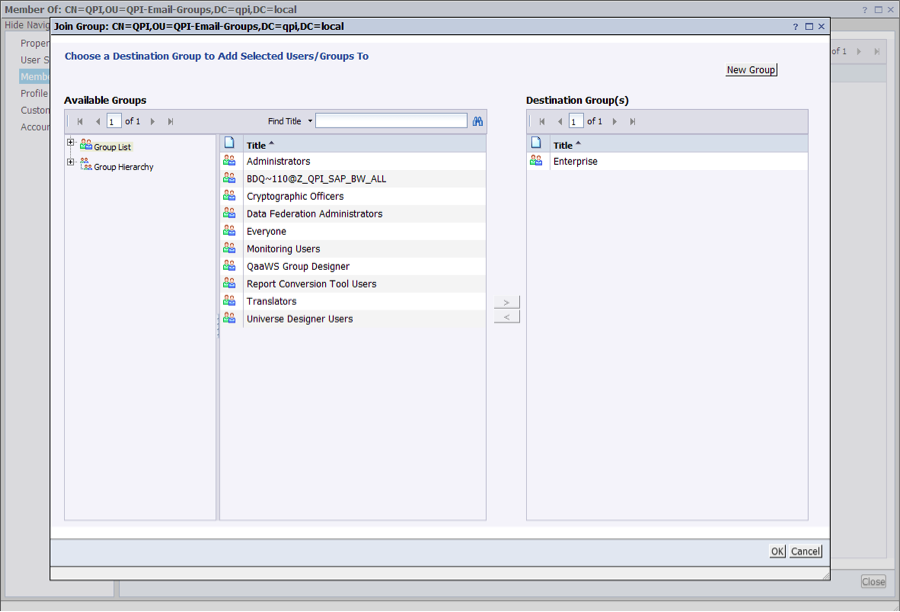
Después de esto, incluiremos el grupo LDAP dentro del grupo "Enterprise" recién creado:
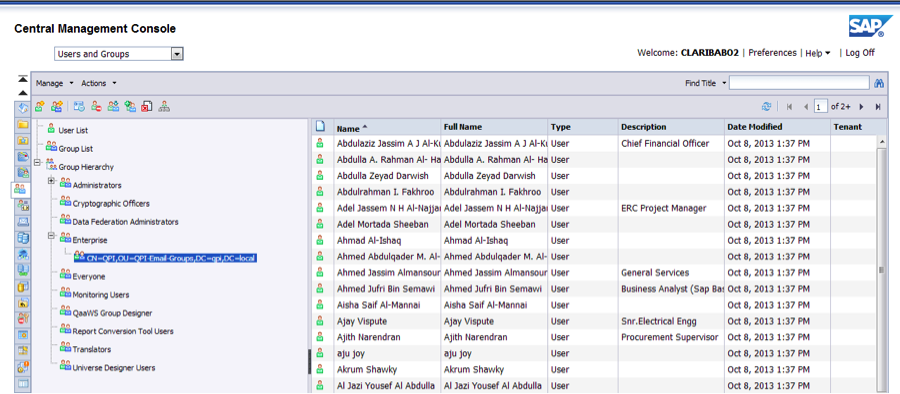
Esta es la salida final:
La forma de probar que todo salió bien es iniciar sesión con el método de autenticación LDAP y comprobar si se accede:
Si bien puede parecer un proceso largo, realmente no toma mucho tiempo y la ventaja percibida para el usuario final es grande, así que animo a todos a implementarla en todas las empresas que implementan LDAP.
Por favor, no dude en escribir en la sección de comentarios si tiene alguna pregunta.